Please check the detailed schedule for your time zone.
An ideal introduction to vulnerability exploitation on 32-bit ARM Linux platform, spanning from ARM32 assembly all the way to Return Oriented Programming (ROP), Infoleaks and defeating stack cookies.
ABSTRACT
The ARM IoT Exploit Laboratory is a newly updated class, focusing on vulnerability development for commercially sold 32-bit ARM IoT devices - Routers, Security cameras, Network video recorders, VoIP phones and several other "smart" appliances running on ARM SoCs. Students shall learn how to analyse, emulate and exploit the firmware on a variety of ARM IoT devices. The class starts with extracting the firmware directly from the devices, moves on to creating an emulated test environment for fuzzing and debugging, and writing end to end exploits for the devices. Students shall also get hands-on training on writing ROP chains and developing infoleaks for bypassing DEP and ASLR. The class features an array of hardware targets of varying complexity. Students shall have ample time for hands on exercises to sharpen their exploitation skills. The class concludes with a preview of ARM64 and key differences between ARM32 and ARM64.
INTENDED AUDIENCE
- Pentesters working on ARM embedded environments. (SoCs, IoT, etc)
- Red Team members, who want to pen-test custom binaries and exploit custom built applications.
- Bug Hunters, who want to write exploits for all the crashes they find.
- Members of military or government cyberwarfare units.
- Members of reverse engineering research teams.
- People frustrated at IoT devices to the point they want to break 'em!
TRAINING FEEDBACK:
I would say the materials from slides, notes, delivery and labs were well-thought and strategically spread out for the duration of the training. It was like ARM basics to advanced on steroids kind of class. All I wish is more trainings of this calibre that other instructions (from other places or on-demand courses) would be able to provide. The certification classes should follow Exploitlabs' imprint in conducting a training. Everything he has shown us were up-to-date material and nothing short of excellence. I have not seen such kind of training before. Such superb training will elevate people in the IT industry to another level whether they are in the security or software engineering side of things. It also helps that Saumil is a seasoned veteran teacher who I can only aspire to be if ever I teach students formally one day.
KEY LEARNING OBJECTIVES
- An introduction to essential ARM32 architecture and assembly.
- An introduction to ARM32 IoT devices.
- Firmware Extraction via UART and flash memory.
- Introducing the EMUX Firmware Emulation Framework.
- How to emulate an IoT device in EMUX.
- Exploiting vulnerabilities in the IoT device.
- Bypassing exploit mitigation technologies - DEP, ASLR and Stack Cookies.
- Practical ARM ROP chains.
- Customised ARM shellcode.
- Overcoming limitations - payload size, bad characters, encodings.
- Exercises, exercises and more exercises
- The Lab environment is a mixture of physical ARM hardware and EMUX Docker images.
COURSE DETAILS
AGENDA
Part 1 - ARM32 Exploitation and Shellcode
- An introduction to essential ARM32 architecture and assembly language.
- EXERCISE - Learn ARM assembly by compiling and reverse engineering binaries.
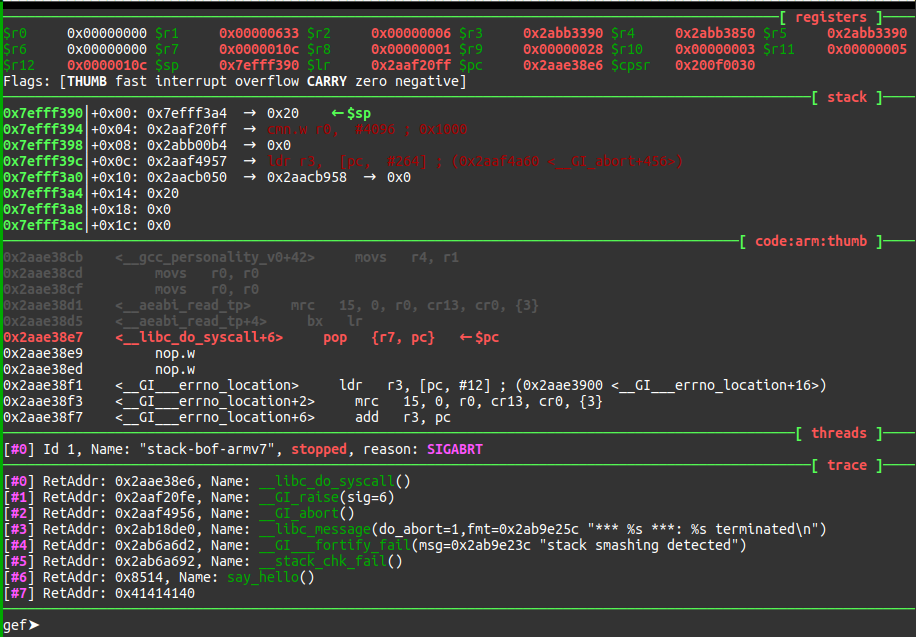
- EXERCISE - Using GDB for debugging ARM ELF binaries.
- An introduction to ARM32 IoT devices.
- Introducting the EMUX Firmware Emulation Framework.
- Debugging the emulated IoT device.
- Memory Corruption
- Exploiting Stack Overflow conditions in ARM binaries.
- Writing customised ARM shellcode.
- EXERCISE - end to end stack overflow exploit.
Part 2 - Overcoming Exploit Mitigation Technology
- Bypassing exploit mitigation technologies - DEP and ASLR.
- Practical ARM ROP chains.
- Attacking the actual hardware.
- Overcoming cache coherency issues.
- Overcoming limitations in the exploit payloads - size, bad characters and encodings.
Part 3 - In-depth Infoleaks and defeating Stack Cookies
- Case Study of a production web server exploit.
- Turning a memory corruption bug into an Infoleak bug.
- Hit Tracing the target looking for Infoleak candidates.
- Leaking base and stack addresses from the target process.
- Practical approach to brute forcing Stack Cookies/canaries.
- End to end exploit with infoleak and stack cookie bypass.
Part 4 - A preview into ARM64
- Key differences between ARM32 and ARM64
- Basics of ARM64 assembly
- An overview of the 64-bit process memory layout
- ARM64 Registers and their purpose
- Limitations and opportunities in ARM64 exploits
- Functions on ARM64 vs ARM32
Exploitation hands-on exercises
- EXERCISES - three hardware targets to emulate and exploit.
- BONUS CHALLENGES - for those hungry for more.
Part 5 - Firmware Extraction & Emulation
- Under the hood - a tour of the circuit boards, pins, interfaces and flash chips.
- Obtaining the firmware via UART, bootloader or an EEPROM programmer.
- Unpacking the firmware and static analysis.
- How to emulate an IP camera in EMUX.
- Matching the device - choosing the right CPU to emulate.
- Matching the device - compiling a custom kernel.
- EXERCISE - emulate a home router in EMUX.
KNOWLEDGE PREREQUISITES
- A conceptual understanding of how functions work in C programming
- Knowledge of how a stack works, basic stack operations
- Familiarity with GDB
- Not be allergic to command line tools.
- If none of the above apply, then enough patience to go through the pre-class tutorials.
- SKILL LEVEL: ADVANCED
REQUIREMENTS
Hardware
- A working laptop (no Tablets, no iPads)
- Intel Core i5 (equivalent or superior) required
- 16GB RAM required, at a minimum
- Wireless network card
- 40 GB free Hard disk space
Software
- Linux / Windows / macOS desktop operating systems
- Docker installed and working
- Command line git client installed and working
- Administrator / root access MANDATORY
ABOUT THE TRAINER
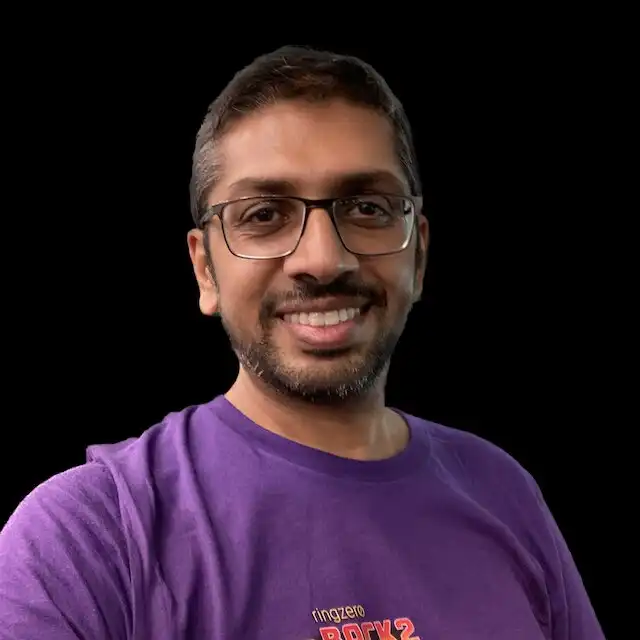
Saumil is an internationally recognised speaker and instructor, having regularly presented at conferences like Blackhat, RSA, CanSecWest, PacSec, EUSecWest, Hack.lu, Hack-in-the-Box, Deepsec and others. He has authored two books titled "Web Hacking: Attacks and Defense" and "The Anti-Virus Book".
Saumil graduated with an M.S. in Computer Science from Purdue University, USA and a B.E. in Computer Engineering from Gujarat University. He spends his leisure time breaking software, flying kites, traveling around the world, and taking pictures.

Virtual Training Schedule
| July 20 | Saturday | Live Lecture (3h) |
| July 21 | Sunday | Live Lecture (3h) |
| July 22 | Monday | Live Lecture (3h) |
| July 23 | Tuesday | Live Lecture (3h) |
| July 24 | Wednesday | Live Lecture (3h) |
| July 25 | Thursday | Live Lecture (3h) |
| July 26 | Friday | Live Lecture (3h) |
Session Timings
| 3 am - 6 am | US Eastern Time |
| 8 am - 11 am | UK BST |
| 9 pm - 12 pm | Europe CEST |
Labs and Discord Channel
24 x 7 throughout the class, and beyond!