QEMU Internals, Instrumentation and Fuzzing
Antonio Nappa
Virtual Training | July 21 - 27 | 32 hours
Please check the detailed schedule for your time zone.
QEMU Internals, Instrumentation and Fuzzing will dive deep into the QEMU universal executor TCG and teach how to model new devices and fuzz them.
ABSTRACT
QEMU Internals, Instrumentation and Fuzzing is a 4 day hands-on course where participants will learn about the fundamentals of emulation and fuzzing, how to emulate a custom device in QEMU from the ground up, and how to instrument it for fuzzing and vulnerability research.
We will dive into QEMU, one of the most powerful software tools designed for emulation and fuzzing, to gain a deep understanding of its architecture and design principles. We'll cover machine types, hardware emulation, and how to write your own platform to emulate and fuzz.
Students will use AFL++, Hongfuzz and some handcrafted examples for testing large software systems for vulnerabilities. We will apply persistent fuzzing, mutational fuzzing and evolutionary fuzzing on real world firmware examples including CANBUS, Fitness devices, Media Players, Networked RTOS based systems, peripheral and bus fuzzing techniques such as USART, UART, baseband, routers, and device sensors.
The class features several hands on exercises where participants will gain an understanding of memory vulnerabilities in IoT devices and how to write exploits, as well as managing responsible disclosure and vulnerability mitigation.
By the end of the course, participants will have a unique set of skills and knowledge from different fields such as emulation of custom embedded systems, instrumented fuzzing, and dynamic analysis, all with a single goal: to find security vulnerabilities.
INTENDED AUDIENCE
- Members of internal penetration testing teams to find and exploit vulnerabilities in bare metal embedded IoT devices
- Vulnerability researchers interested in implementing custom emulation and fuzzing harnesses for proprietary IoT devices
KEY LEARNING OBJECTIVES
- Fundamental concepts of emulation and fuzzing as useful tools in vulnerability research
- QEMU, Panda, AFL++, Hongfuzz, Avatar2
- Set up an emulation and fuzzing environment for the course using QEMU and AFL/AFL++
- QEMU architecture and design principles, including machine types and hardware emulation
- QEMU execution modes and performance optimization using Panda or Avatar2
- Static and dynamic fuzzing techniques, and fuzzer injection into proprietary firmware
- Apply emulation and fuzzing techniques to real-world targets:
- IoT devices, CANBUS fuzzing, Media Players, Network Services, Fitness devices, Real-Time Tasks
- Knowledge of peripheral and bus fuzzing such as USART, UART, baseband, routers, device sensors
- Identify memory vulnerabilities and write exploits, and understand responsible disclosure and vulnerability mitigation
- Understand how fuzzing+emulation are the game changer for vulnerability research
COURSE DETAILS
AGENDA
Day 1: Introduction
- Static analysis
- Binary lifting
- From lifting to execution
- Examples, P-Code, Intro to TCG
- Hands-on -> Kunai, disasm and lift
- Hands-on -> Kunai, IR analysis
- TCG Internals
- Hands-on tracking code through the TCG: registers
- Hands-on tracking code through the TCG: jumps
- Hands-on tracking code through the TCG: Code coverage
Day 2: Introduction to QEMU architecture and design principles
- Overview of QEMU components and their interactions
- Understanding QEMU machine types and hardware emulation
- QEMU execution modes and performance optimisation
- Hands-on exercise: Building and customising a QEMU machine type for the ST Nucleo L452RE board
- Hands-on exercise: Writing the UART for the ST Nucleo L452RE board
- Case studies of successful emulation and fuzzing in vulnerability research (e.g., IoT devices, web applications)
- Hands-on exercise: Compare Avatar2 approach with Python vs. pure QEMU board emulation
- Fuzzing with QEMU
- Going through a fuzzing harness
- Hands-on exercise: Finding and exploiting vulnerabilities in our RTOS based firmware on the ST Nucleo L452RE board
- Hands-on exercise: Writing the harness for a specific component
Day 3: Pebble watch and RebbleOS on QEMU
- Fuzzing campaign
- Code analysis
- Harness
- Checking crashes
- Bugs and patches
- CAN Bus fuzzing
- Can Bus crash course
- Setup messages
- Fuzzing campaign
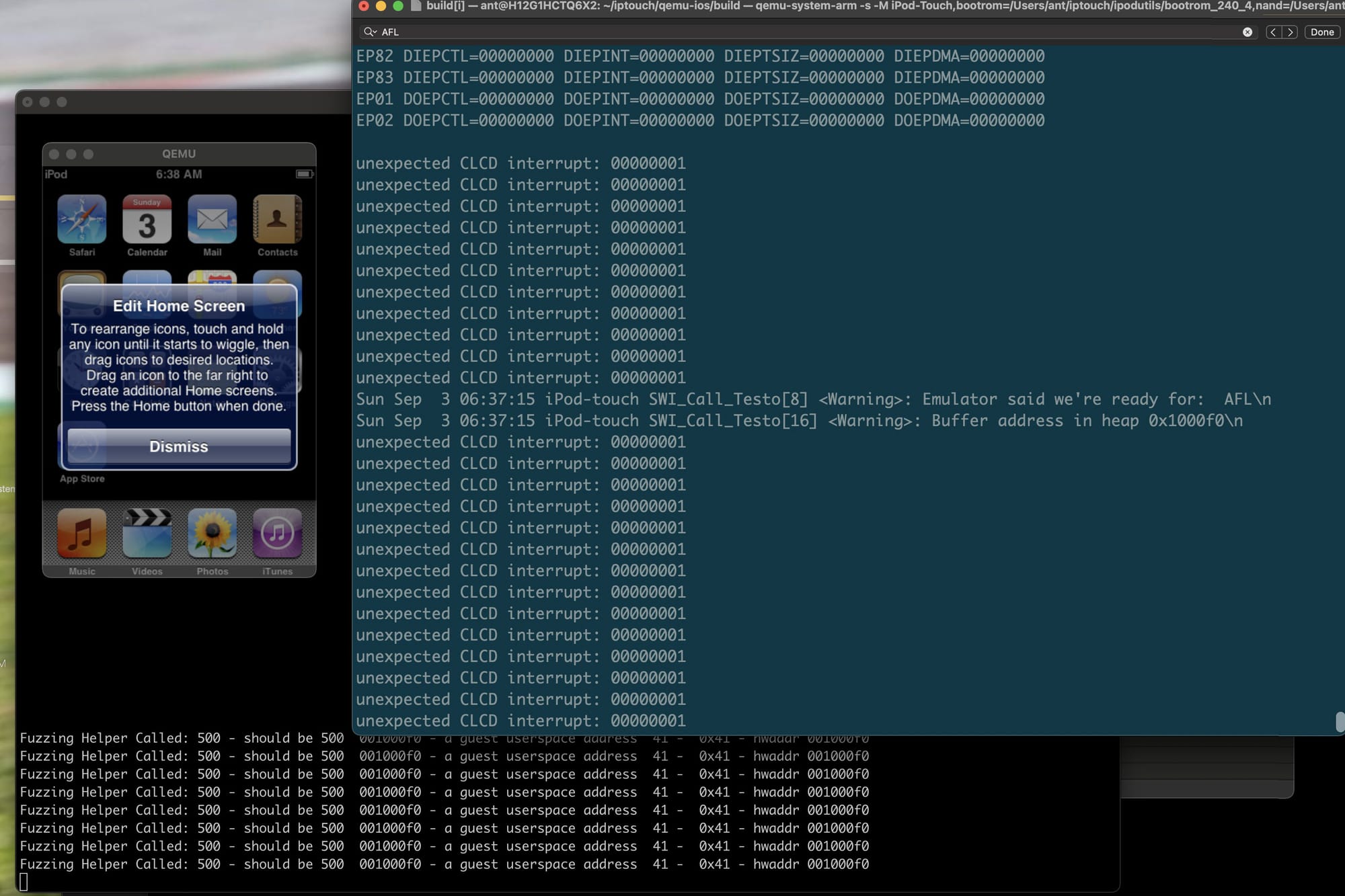
Day 4: iOS Devices
- Approaching closed source firmwares iPod Touch 1/2g
- Finding code caves
- Injecting and testing code
- Re-writing the AFL harness
- iPhone 11 approach with syscalls
KNOWLEDGE PREREQUISITES
C Programming, GDB and static analysis
SYSTEM REQUIREMENTS
Hardware Requirements
- Laptop capable of running Linux or macOS
- 16 GB RAM preferred
- Approximately 180GB of free disk space if you want to download the Docker container locally
Software Requirements
- Docker (if you wish to execute the labs locally) and VSCode (for Linux/macOS)
- Ghidra 10.3
ABOUT THE INSTRUCTOR
Antonio Nappa, Ph.D is the Application Analysis Team Leader at Zimperium Inc. Before joining Zimperium he worked at Brave Software and Corelight.
Antonio has been active in the cybersecurity industry since 17 years. He has been a visiting scholar at UC Berkeley, EURECOM, VSB-TUO. He has published more than 15 papers in international peer-reviewed venues. He is also an inventor and a well recognized adjunct professor at UC3M Madrid.
He is co-author of: Fuzzing Against the Machine: Automate vulnerability research with emulated IoT devices on Qemu, Packt Publishing 2023.
Since the DEFCON 2008 Finals with the Guard@Mylan0 team, he never goes to sleep with a segfault.

Virtual Training Schedule
| July 21 | Sunday | Live Lecture (3h) |
| July 23 | Tuesday | Live Lecture (3h) |
| July 24 | Wednesday | Live Lecture (3h) |
| July 25 | Thursday | Live Lecture (3h) |
| July 26 | Friday | Live Lecture (3h) |
| July 27 | Saturday | Live Lecture (3h) |
Session Timings
| 8 am - 11 am | US Pacific Time |
| 11 am - 2 pm | US Eastern Time |
| 4 pm - 7 pm | UK BST |
| 5 pm - 8 pm | Europe CEST |
Labs and Discord Channel
24 x 7 throughout the class, and beyond!