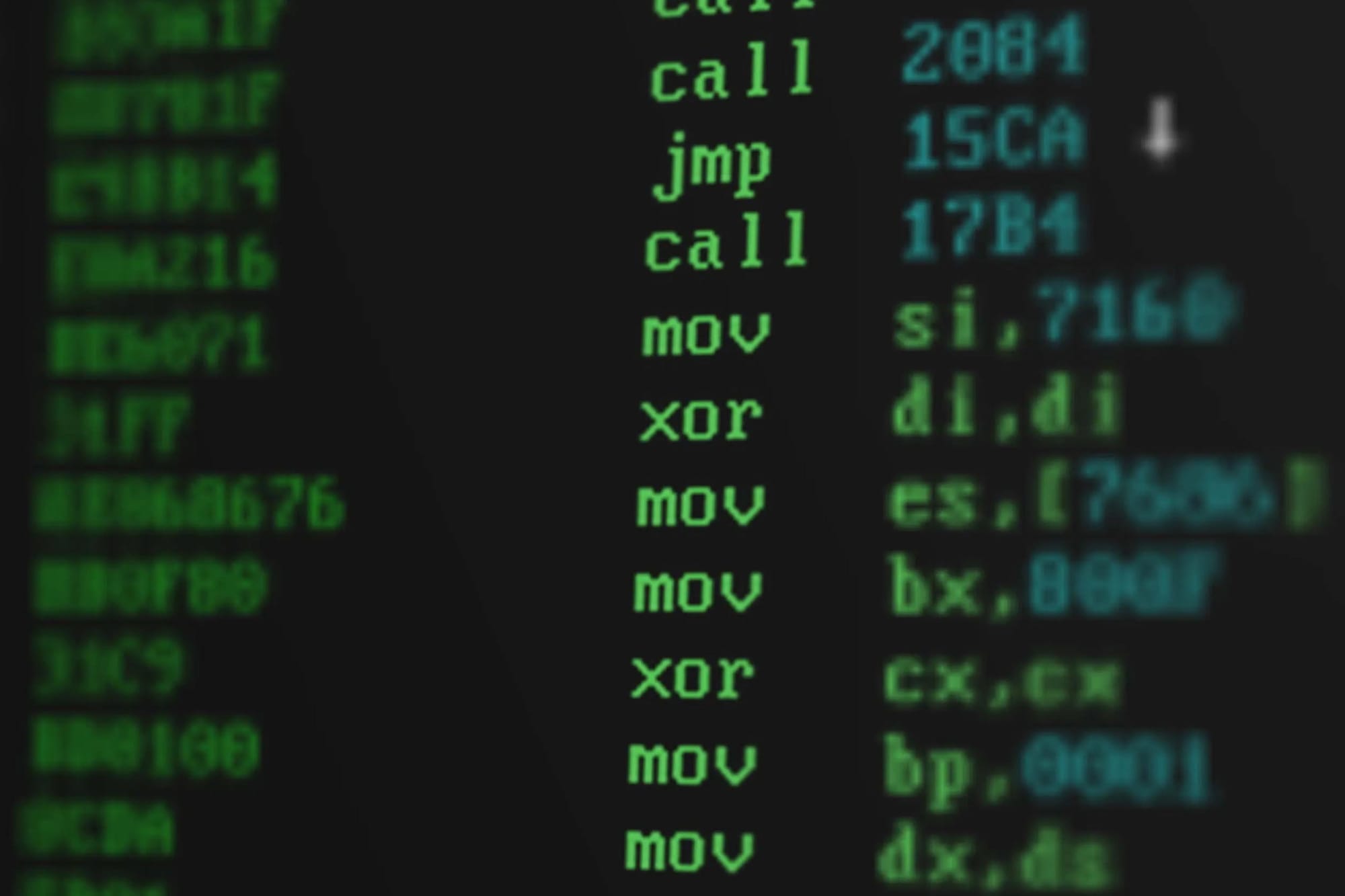
Disassemble binaries, read x86-64 assembly and debug binaries in WinDBG and GDB. Learn the fundamentals of Assembly Language with Xeno Kovah.
ABSTRACT
This class teaches you how to disassemble binaries, read x86-64 assembly language, and debug black-box binaries in WinDbg and GDB. This knowledge of assembly is the fundamental skill which is required to learn reverse engineering and vulnerability exploitation. Reverse engineering is in turn a fundamental skill which is required for malware analysis and vulnerability hunting.
ONE OF A KIND CLASS FORMAT
Because we give you all the lecture and lab materials and videos after class, what you're really paying for is support from the instructor! So you'll be entitled to keep asking up to 20 questions after class, with 1-2 hour turnaround answers (after accounting for time-zone differences.) This lets you keep productively working through the material if you run out of time at the conference. If you'd like to learn more about the benefits of this style of class delivery, please read this blog post.
KEY LEARNING OBJECTIVES
- Learn the most common assembly instructions, which cover > 96%+ of all code found in most programs.
- Learn about the 16 Intel x86-64 general purpose registers + RFLAGS.
- Understand the at time confusing or counter-intuitive compiler-isms of both Microsoft Visual Studio, and GCC which lead to particular patterns in executables' assembly.
- Learn to debug and analyze executables which you don't have the source code for, in both WinDbg and GDB.
- Learning how to write C code and disassemble it to see what instructions were generated. But also learning how to write assembly to see how it behaves, or even raw bytes to see how the assembler and processor interprets it.
- Being comfortable with Reading The Fun Manual (RTFM!) to go seek out the most accurate details of how things work.
- Reverse engineer the black box Carnegie Mellon "Binary Bomb Lab", which has changed the lives of so many students (the instructor included!) This is a major hands-on reverse engineering exercise (which can take anywhere from 2 hours to 2 weeks!) which has been shared the world over by thousands of students. This gives you something substantive to chew on even after class to really reinforce your understanding and capability to read assembly.
COURSE DETAILS
AGENDA
- Introduction
- About this class
- Optional refresher: binary to hex to decimal
- Optional refresher: two's complement negative numbers
- Optional refresher: C data type sizes
- Background: Endianness
- Computer Registers
- Memory hierarchy
- x86-64 general purpose registers
- Intel recommended register conventions
- Your First Instruction
- No-Operation (not)
- The Stack
- Overview
- New instructions: push & pop
- RoX0r Arcade: The RSP Game:
- Level 1: Canonical orientation, rbp at top, rsp at bottom
- Level 2: Canonical orientation, rbp and rsp move around
- Level 3: Canonical or flipped orientation, rbp and rsp move around
- Level 4: Four possible orientations, rbp and rsp move around
- Calling Functions
- CallASubroutine1.c: New Instructions: call, ret, mov, add, sub
- Stack frame single-step slideware walkthrough
- Stack frame single-step VisualStudio walkthrough
- RoX0r Arcade: Dark Mathemagic:
- Level 1: Basic mov, add, sub w/o calculator
- Level 2: mov, add, sub w/ calculator
- Local Variables
- SingleLocalVariable.c
- Mystery Listery 3 Solved!
- ArrayLocalVariable.c, New Instructions: imul, movsx, movzx
- StructLocalVariable.c
- RoX0r Arcade: Dark Mathemagic:
- Level 1: movzx
- Level 2: movsx
- Function Parameter Passing
- Pass1Parameter.c
- TooManyParameters.c
- Mystery Listery 2 Solved!
- 64-bit Calling Conventions
- 32-bit Calling Conventions
- Mystery Listery 1 Solved!
- SpecialMaths.c, New instructions: lea
- RoX0r Arcade: Dark Mathemagic:
- Level 1: lea
- Control Flow
- GotoExample.c, New instructions: jmp
- IfExample.c, New instructions, "jcc", cmp
- IfExample2.c
- SwitchExample.c
- RoX0r Arcade: 1 step forward, 3 steps back: Jumps
- Level 1: jz/je, jnz/jne
- Level 2: ja/jnbe, jna/jbe, jb/jnae, jnb/jae
- Level 3: jg/jnle, jng/jle, jl/jnge, jnl/jge
- Boolean Logic
- Refresher: Boolean logic
- BooleanBecause.c, New instructions: and, or, not, xor
- ForLoopNoRet.c, New instructions: inc, dec
- BitmaskExample.c, New instructions: test
- RoX0r Arcade: Dark Mathemagic:
- Level 1: and, or, xor, not
- Level 2: inc, dec
- RoX0r Arcade: 1 step forward, 3 steps back: Jumps w/ test
- Level 1: test, js, jns
- Bit Shifting
- ShiftExample1.c, New instructions: shl, shr
- ShiftExample2Unsigned.c
- ShiftExample3Signed.c, New instructions: cdq, sar
- RoX0r Arcade: Dark Mathemagic:
- Level 1: shl/sal, shr, sar
- Multiply and Divide
- MulDivExample.c, New instructions: div, idiv
- RoX0r Arcade: Dark Mathemagic:
- Level 1: mul + imul, 1-operand form
- Level 2: mul + 1, 2, and 3-operand forms of imul
- Level 3: div + idiv
- CISC Delight: REPeatable Instructions
- ArrayLocalVariable2.c, New instructions: rep stos
- ThereWillBe0xb100d.c
- JourneyToTheCenterOfMemcpy.c: New instructions: rep movs
- RoX0r Arcade: DarkMathemagic: BOSS LEVEL!!!
- YOU VS. ACCUMULATOR!!!
- Choose Your Own Adventure!
- Here, if you mostly care about Windows, GOTO Windows Binary Debugging
- Else, if you care about *NIX systems, you can learn about AT&T syntax and see all of the previous code again as compiled by GCC instead
- Windows Binary Debugging
- Windbg tutorial
- GOTO Learning to Fish: Read The F*n Intel Manual!
- Looking at all those examples on Linux!
- Intel vs. AT&T assembly syntax
- Separate videos for all of the following in Linux:
- CallAFunction1.c, SingleLocalVariable.c, ArrayLocalVariable.c, StructLocalVariable.c, Pass1Parameter.c, TooManyParameters.c, SpecialMaths.c, GotoExample.c, IfExample.c, IfExample2.c, SwitchExample.c, BooleanBecause.c, ForLoopNoRet.c BitmaskExample.c, ShiftExample1.c, ShiftExample2Unsigned.c, ShiftExample3Signed.c, MulDivExample.c, ArrayLocalVariable2.c, ThereWillBe0xb100d.c, JourneyToTheCenterOfMemcpy.c
- RoX0r Arcade: DarkMathemagic: BOSS LEVEL!!!
- YOU VS. GNASTY ACCUMULATOR!!!
- Learning to Fish: Read The F*n Intel Manual!
- Learn to read the FUN manual!
- Learning to Fish: Writing Assembly
- Writing x86-64 assembly in Visual Studio
- Writing x86-64 assembly in GCC
- The Most Important Assembly Exercise You'll Ever Do: Binary Bomb Lab
- Bomb Lab Intro
- Do the Bomb Lab in either WinDbg or GDB
- Conclusion
REQUIREMENTS
Hardware Requirements
- A PC or an x86 Mac (class won't work with an M1 Mac!) capable of running 2 VMs at a time with ideally 4 GB of dedicated RAM per VM.
- Headphones for watching videos, (preferably over-ear so you're not disturbed as the instructor is walking around the class answering individuals' questions).
Software Requirements
- Administrator privileges to install virtualization software on your machine.
- A PC with VMWare Workstation or an x86 Mac with VMWare Fusion (the free "Player" versions are fine).
- ISO for installing 1 instance of x86-64 Windows 10 (30 day trial version is fine).
- ISO for installing Ubuntu Linux 20.04 (if you choose to learn the optional AT&T assembly syntax material).
- A link to a software setup guide will be sent before class, and the student should install before class to maximize time available for interaction with the instructor.
- Other software includes Visual Studio 2019, the Windows Software Development Kit (SDK), the Windows Driver Development Kit (WDK), and WinDbg.
- For the optional Linux material, it includes gcc and gdb.
ABOUT THE INSTRUCTOR
Xeno began leading Windows kernel-mode rootkit detection and defense research projects at MITRE in 2009, before moving into research on BIOS security in 2011. His team's first public talks started appearing in 2013, which led to a flurry of presentations on BIOS-level vulnerabilities up through 2014. In 2015 he co-founded LegbaCore. And after presenting a firmware worm that could spread between Macs via Apple's EFI-based BIOS and Thunderbolt Ethernet adapters, he ended up working for Apple. There he worked on securing all the lesser-known firmwares on Macs and peripherals - everything from 3rd party GPUs to SecureBoot for monitors! He worked on the x86-side of the T2 SecureBoot architecture, and his final project was leading the M1 SecureBoot architecture - being directly responsible for designing a system that could provide iOS-level security, while still allowing customer choice to trust arbitrary non-Apple code such as Linux bootloaders. He left Apple in Dec 2020 after the M1 Macs shipped, so he could work full time on OpenSecurityTraining2.